Overview of Proarc EDMS Online Security
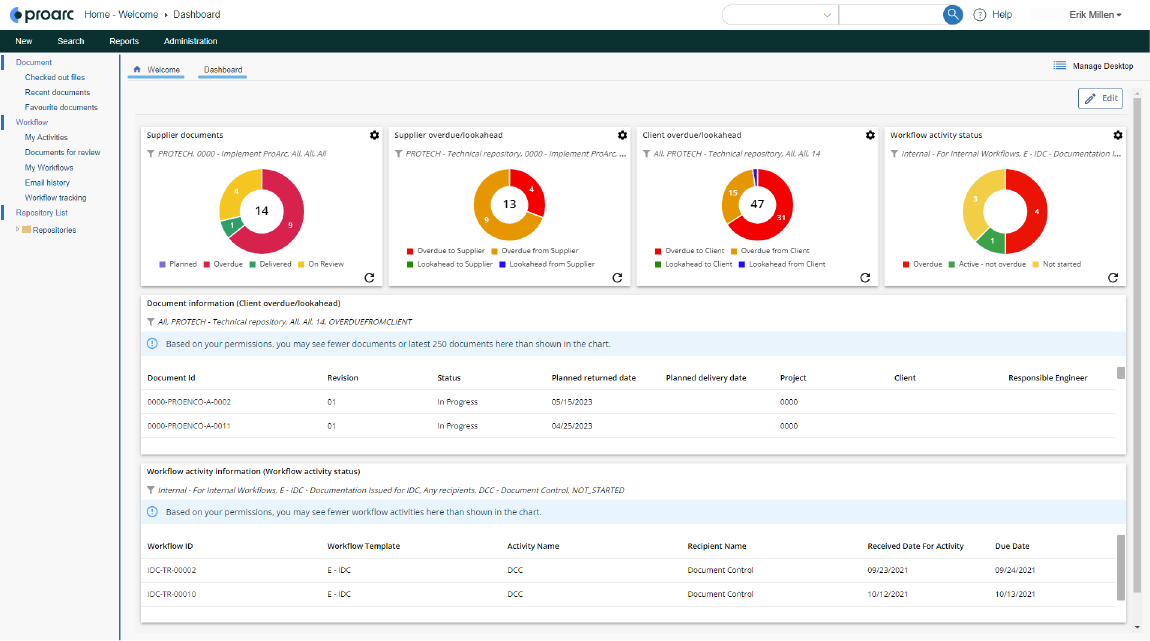
Proarc Online is a business-critical engineering document management SaaS solution provided by Ascertra. Major industrial construction projects rely on Proarc Online day-to-day to organize, plan, execute, collaborate, track, and deliver documentation. They demand a system that is reliable, secure, and responsive around the clock. Proarc Online provides this level of service because every aspect of the system, from software development to the hosting infrastructure, has been designed and configured with these goals in mind.
The foundation for Proarc Online is aligned with the five core pillars of cloud computing architecture: security, reliability, performance, cost optimization, and operational excellence. This article focuses on the key principles, practices, and services used to ensure Proarc Online security.
Security is the central and most important factor in Proarc Online’s architecture. Protecting Proarc infrastructure, applications, and data from rapidly evolving threats by adopting a "zero trust" approach is key to Proarc Online security. The system is designed and operated to provide multiple layers of security across its infrastructure, applications, and data.
Identity & Access Management
Identity and access management ensure only the right people and roles access your system and information and is a priority focus area for Proarc Online. Practices and applications employed in Proarc to ensure identity and access management are secure, include:
- Proarc identity management is implemented with the proven flexible and reliable OpenID Connect protocol; customers are free to choose their own identity providers based on their security needs and policies. Some of the major identity providers Proarc supports include Azure AD, OKTA, Google, and ADFS.
- Multi-factor authentication is a standard feature of Proarc Online, challenging users to provide additional proof of identity beyond their username and password.
- Management of users, groups, and rights to access various applications are strictly controlled using role-based access controls.
- Proarc API access is secured based on the OAuth open standard protocol.
Encryption and Key Management
Securing data—“At Rest” and “In Transit”—is critical. Data security can be compromised when transferring between components, locations, or programs.
- Proarc employs robust data security through cryptography. Data is secured with strong encryption algorithms when in transit and rest by default.
- All the access keys, secrets, and passwords are securely stored and retrieved in runtime with Azure Key vault.
Layered Security
Proarc follows various Azure best practices for network security, adopting a zero-trust approach using strong network controls & virtual network appliances.
- Proarc infrastructure, applications, and interfaces are secured with Virtual LAN, Azure Firewall, Web Application Firewall, and internal IP restrictions.
- Azure Firewall and the web application firewall in the Application gateway help in FQDN filtering and have support for Open Web Application Security Project (OWASP) core rule sets.
- Proarc uses conditional access to resources based on the device, identity, user location, etc.
Detection & Prevention
Proarc leverages Azure’s detection and prevention capabilities to maximize threat protection.
- The logical network segment (DMZ) created for the Proarc platform in Azure provides an additional layer of security that helps in enabling denial of service prevention and intrusion detection/intrusion prevention systems.
- Detailed activity logging and monitoring help in the timely detection of security anomalies.
Securing from Web Vulnerabilities
Proarc is developed to withstand the latest vulnerabilities affecting software applications.
- Proarc is tested for web vulnerabilities using best-of-breed automated vulnerability scanning tools that scan for thousands of vulnerabilities, including the OWASP Top 10 Vulnerabilities.
- The Proarc code base is continuously scanned for vulnerabilities using sophisticated static code analysis tools.
- Proarc assemblies/compositions are also continuously scanned for OWASP Top 10 Vulnerabilities
Proarc is securely built starting from the development environment to the live deployment platform. Security best practices and recommendations are followed to ensure all resources and infrastructure elements within the Proarc Online boundary are secured.
To learn more about Proarc Online and how it helps teams securely execute projects on schedule, reduce risk, and ensure compliance, visit the Proarc EDMS page.